The 5 Hacking NewsLetter 33
Posted in Newsletter on December 25, 2018
Posted in Newsletter on June 24, 2018

Hey hackers! Here are our favorite resources shared this week by pentesters & bug bounty hunters. It covers the week from to the 22th to the 28th of June.
There are some goodies in this one, it was a lot of fun to compile it.
I absolutely LOVE watching these interviews! They’re not too long and remind me of a non technical version of Bugbountyforum’s AMAs.
I am in the process of becoming a full-time pentester/bug bounty hunter/ independant security researcher. This is my passion and a 100% what I want & need, but it involves a lot of work and some loneliness in the sense that almost all people around me do not even understand what I do. So watching these amazing people tell their own stories inspires me to keep going on and makes me feel I’m part of a beautiful community.
Testssl.sh is great and should be used for penetration tests but it has room for improvement for scalability reasons.
In my last corporate job, we sometimes had to test hundreds of targets at the same time and generate a detailed report for all findings. It is impossible to do by reading testssl.sh’s results manually!
So we developped an internal script to run it on as many targets as needed, parse its results and output a CSV file containing:
We could then include this table directly in our reports.
Sadly, I cannot publicly disclose this tool because, although I participated in its development, it is not mine to publish.
So I highly recommend IDontSpeakSSL. It’s very similar: It also parses the results of testssl.sh and generates an HTML report of all the findings.
How re-signing up for an account lead to account takeover by zseano
Bug hunting is a mind game. One of the pitfalls is thinking that, because a target was tested by hundreds of other bug hunters, there were no chances left to find other bugs.
But original thinkers will always find new bugs, and @zseano share with us here his secret: we should develop reflexes like testing from different angles (changing user agents, devices, languages, sessions, etc). Some of these actions may trigger the target to behave differently and introduce new bugs or entry points to attack.
This is an awesome tutorial covering all the basics of subdomain takeover! There’s really nothing to say other than… please read it & take notes!
I also recommend reading this writeup by the same author, which shows how he exploited such a vulnerability on Microsoft Azure.
Reintroducing the Cybersecurity Style Guide: V1.1 by Bishop Fox
This is a comprehensive lexicon of cybersecurity-related terms and acronyms. The first time I came accross words like AMA, OSGi, QA, UX, etc, I was afraid afraid to ask what they mean and did not have enough context to find their meaning using Google. This document would have been a time-saver!
You can find the latest bug bounty writeups in our dedicated page: List of bug bounty writeups.
Only writeups that did not make it to this selection are listed below. This does not mean that they aren’t worth reading, just that they are not BUG BOUNTY writeups. We will soon post more details about how our curation process.
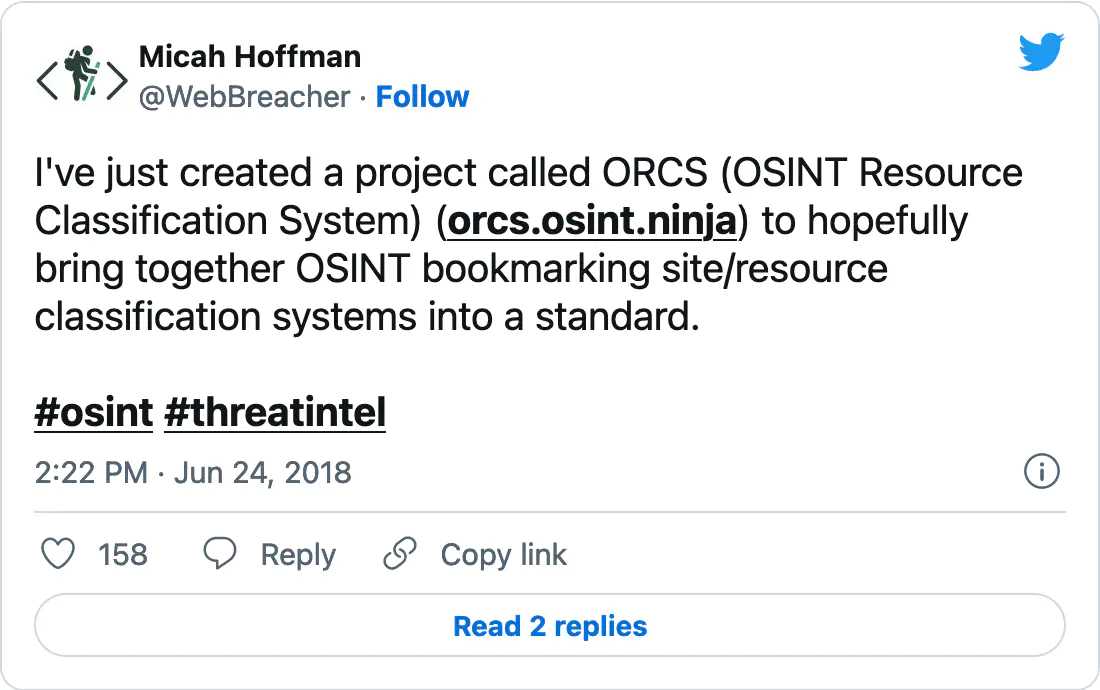
We created a collection of our favorite pentest/bug bounty related tweets shared this week. You’re welcome to read it directly on Twitter.
Have a nice weekend folks!
If you enjoyed reading this, please consider sharing it, leaving a comment, suggestions, questions…