The 5 Hacking NewsLetter 33
Posted in Newsletter on December 25, 2018
Posted in Newsletter on June 24, 2018

Hey hackers! Here’s our collection of the best resources shared this week by pentesters & bug bounty hunters. It covers the week from to the 15th to the 22th of June.
Have a good reading!
This is not a new technique, but it’s a good exploitation scenario to show one pratical risk of XSS vulnerabilities. From experience, using <script>alert(0)</script> in pentest reports is not very convincing for clients.
I try to always include proof of concepts that show what exactly is possible on the particular context being tested: redirection, iframe inclusion, cookie theft, credentials theft from the browser, etc.
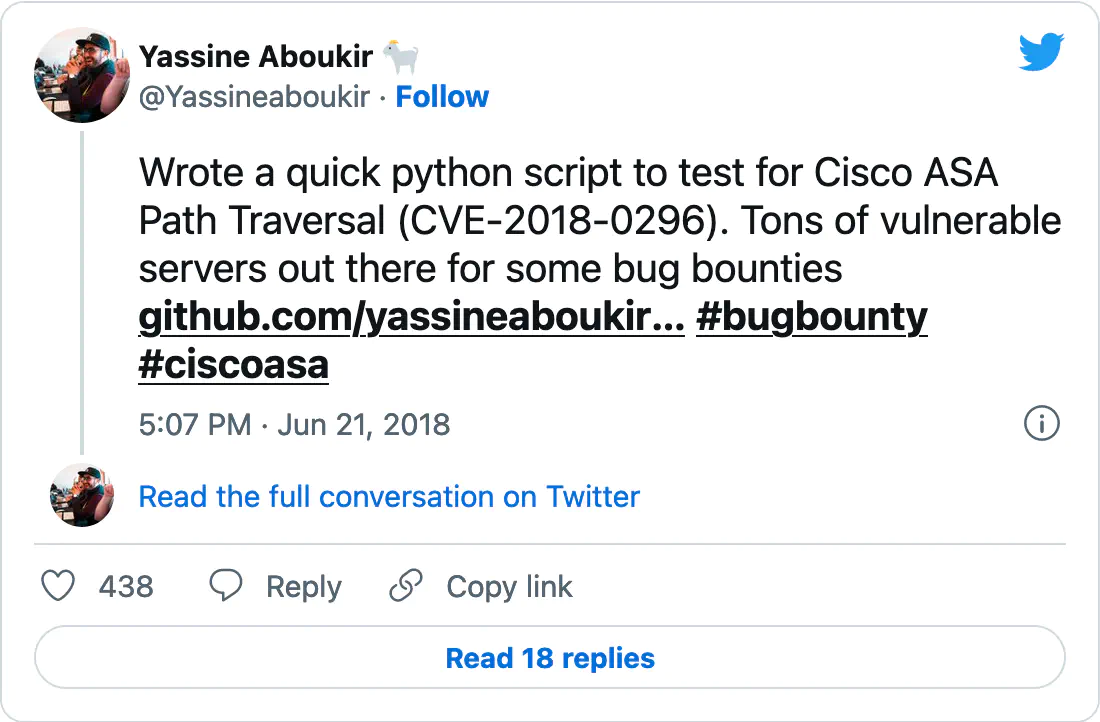
This is another example of why recon is the most important part of bug bounty hunting. The process is nicely detailed, from subdomain enumeration to analyzing results and detecting the vulnerable server, and will (maybe) help you improve your own methodology.
Area 41 2018, especially:
- Thomas Debize: Modern Pentest Tricks For Faster, Wider, Greater Engagements
- Lazy Ways To Own Networks by Nicolas Heiniger
- Red Team: Stories From The Trenches by Stefan Friedli and Michael Schneider
- Defense-In-Depth Techniques For Modern Web Applications by Spagnuolo and Weichselbaum
- Amit Dori: Chrome & WebRTC -eq Problems
I particularly loved Thomas Debize’s talk “Modern Pentest Tricks For Faster, Wider, Greater Engagements”! It presents a lot of valuable tips & tools for penetration testers, that I haven’t seen anywhere else. If you are a professional pentester (or want to be), these tricks would make your life easier.
Breaking into Information Security: Learning the Ropes 101 by Andrew Gill
This is a great (and free!) book for anyone starting in InfoSec or who wants to specialize in penetration testing or bug bounty hunting. There’s A LOT to learn, but don’t be overwhelmed. Just start with this introductory book, practice what you learn, read other technical books like Web Hacking 101 and continue practicing.
For anyone starting in bug bounty or thinking of doing it full time, knowing what can go wrong and how to deal with it is primordial. Start with this blog post, and also track other hunters’ feedback (on Twitter particularly) on their frustrations and which programs do not treat researchers fairly and are better avoided.
You can find the latest bug bounty writeups in our dedicated page: List of bug bounty writeups.
Only writeups that did not make it to this selection are listed below. This does not mean that they aren’t worth reading, just that they are not BUG BOUNTY writeups. We will soon post more details about how our curation process.
See you next time!
If you enjoyed reading this, please consider sharing it, leaving a comment, suggestions, questions…